Painstaking Lessons Of Info About How To Avoid Trojan Virus
Open attachments or links sent via email.
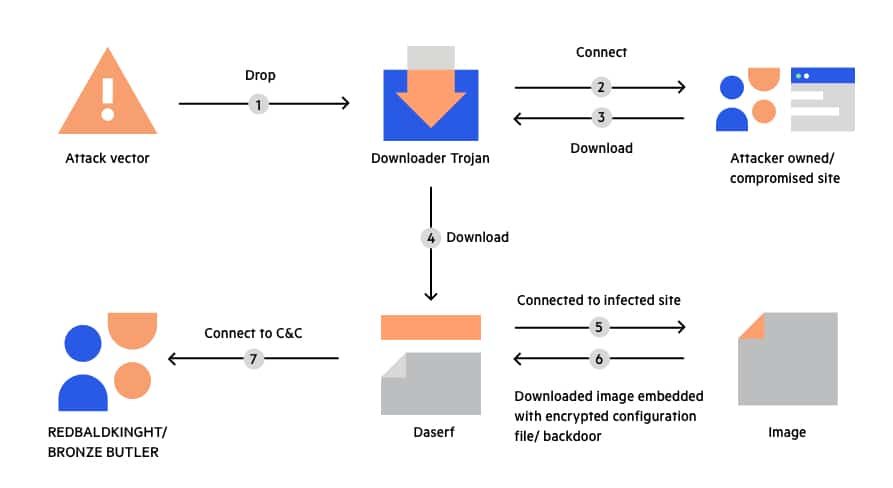
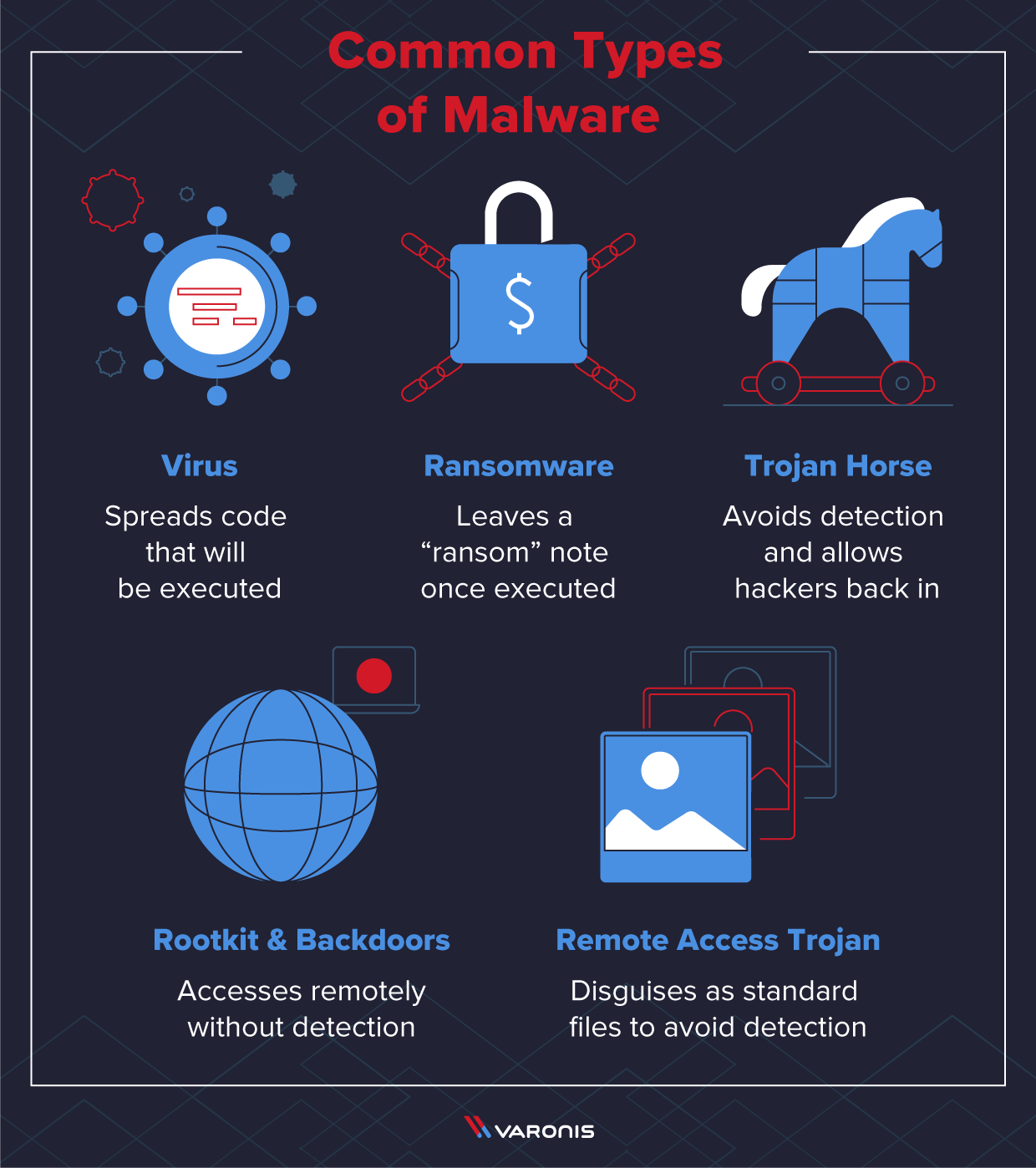
How to avoid trojan virus. Can trojan virus be detected? Up to 18% cash back never download or install software from a source you don’t trust completely. The reason that trojan horses look like legitimate software is because they are so difficult to detect.
How do you remove a trojan virus from computer for free? Setup cloud accounts using email addresses. Here are some tips to help protect your device and prevent malware:
Up to 20% cash back this can help prevent an infected image from turning into a virus on your computer. How to remove malware such as a virus, spyware, or rogue security software 1. Patch your operating system and applications.
You can protect yourself against trojan. In order to detect, isolate and remove trojan signatures,. Here are ways to avoid malware:
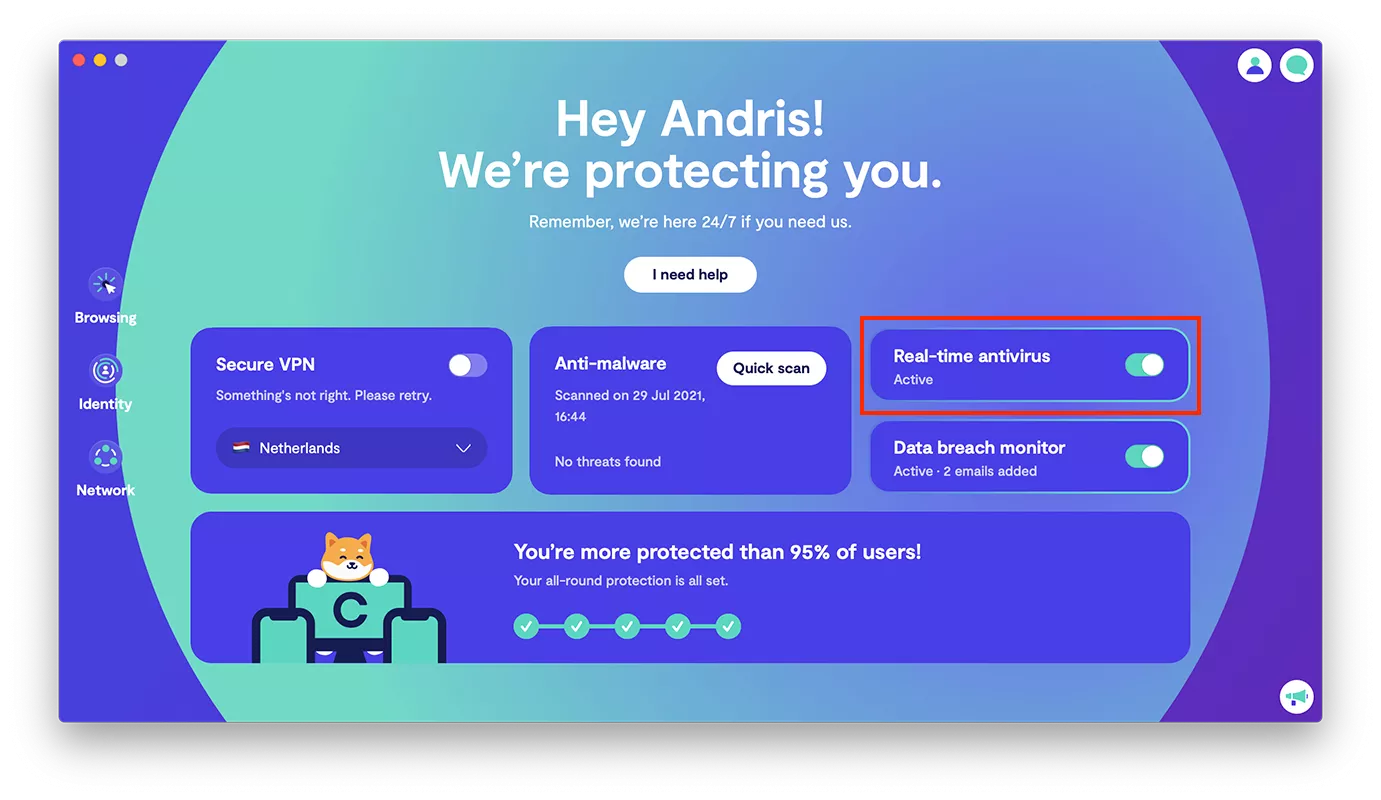
You can run microsoft defender on your computer. You should never fully trust the. The professional service firm deloitte recommends keeping up with developments in cybersecurity technology by employing tactics.
Install the latest updates from microsoft update note a computer virus may prevent you from accessing the. As always, the greatest protection against trojan horse is a mix of complete antivirus protection and solid cybersecurity tactics: Trojan horses are often sent via email attachments in spam emails.
Ad the world's leading digital security software + identity protection. Back up your device files. By having a copy of your files, you may not be able to stop cybercriminals from stealing data.
Removing trojans is a great way to safeguard your computer and privacy, but you must also take steps to avoid them in the future: 10 ways to prevent malware and viruses. Keep your software up to date.
Ad find the top apps to get rid of trojan virus at a price that can't be beaten! Remove trojan horse viruses today. How to protect yourself from virus, malware, trojan and worm?
The second step is to use malwarebytes to remove trojans, viruses, and. · install and update security software, and use a firewall. Never open an attachment or run a program sent to you in an email from.